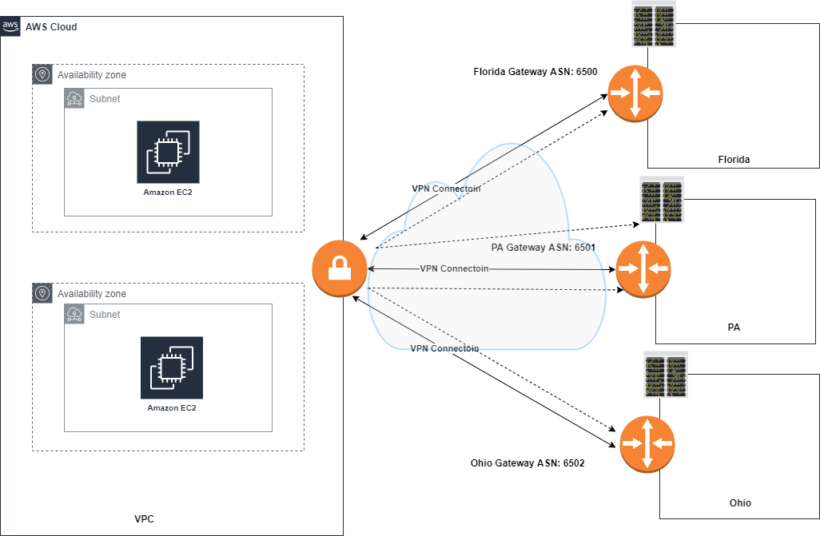
An AWS Client VPN (also known as a remote access vpn) allows a host outside a given network to gain access to private resources across the internet. With the rise of remote work this type of needed configuration has become popular. Every end host will have to create a vpn tunnel to the vpn gateway. If multiple end users at a remote site need network access, creating a site-to-site vpn connection may make more sense.
As shown in the picture below, end users will need some gateway to connect to on the other end. In this guide we will walk through how to setup an aws client vpn using openvpn.
Setting up an AWS Client vpn
Typically, when setting up a remote access vpn connection, most companies will use physical gear sitting in a datacenter. With the explosion of cloud providers such as aws, google cloud and Microsoft azure, many vendors have software instances that can be provisioned to emulate physical gear in the cloud at a more reasonable price.
Openvpn is a virtual private network provider that we will use in aws to set up remote access to the cloud.
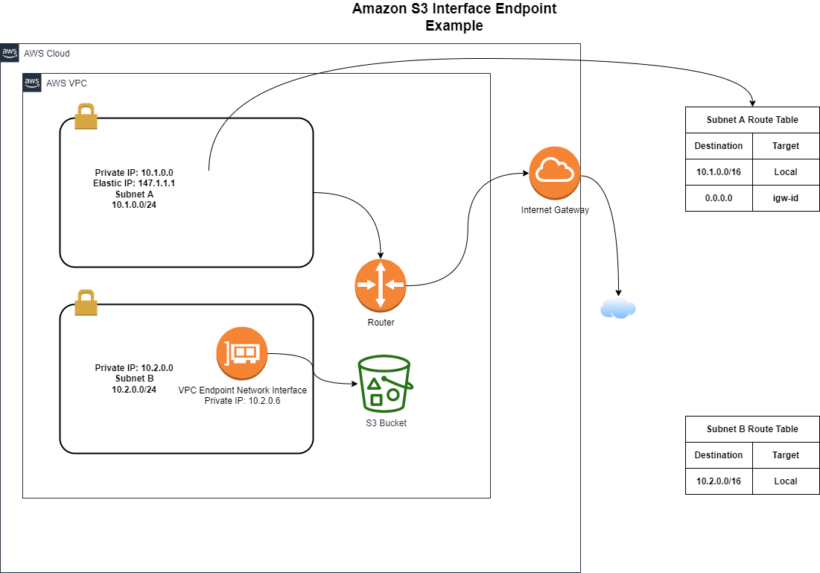
Setting up your vpc
First you want to set up your vpc. Depending on your needs for the cloud this could vary, but let’s set up a simple vpc configuration. I would recommend reading this post here to walk through creating your first aws environment.
Configure OpenVPN from the aws marketplace
Open the AWS Marketplace console after logging in to the AWS Management Console. Then, in the search bar, type OpenVPN Access Server and select the option that best suits your needs.
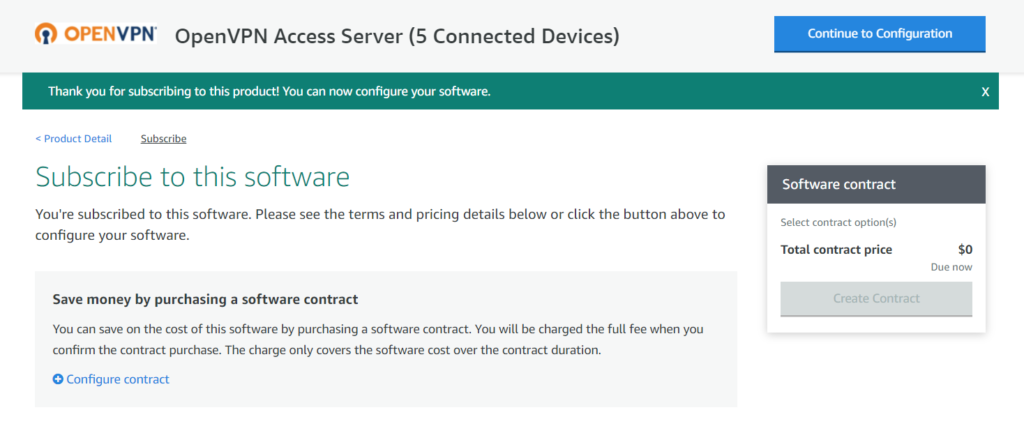
The OpenVPN Access Server (5 Connected Devices) version comes with a 7-day free trial so you can check it out before paying for it. When the free trial period ends, your AWS payment will automatically change to a paid hourly subscription. Other alternatives, such as those billed by the hour or by annual subscription, support a higher number of devices. You can also bring your own driver’s license (BYOL).
To subscribe and configure the product:
First accept the terms and subscribe to the product. You will not be charged during the free trial. Once the trial ends you will be charged on a per hour basis.
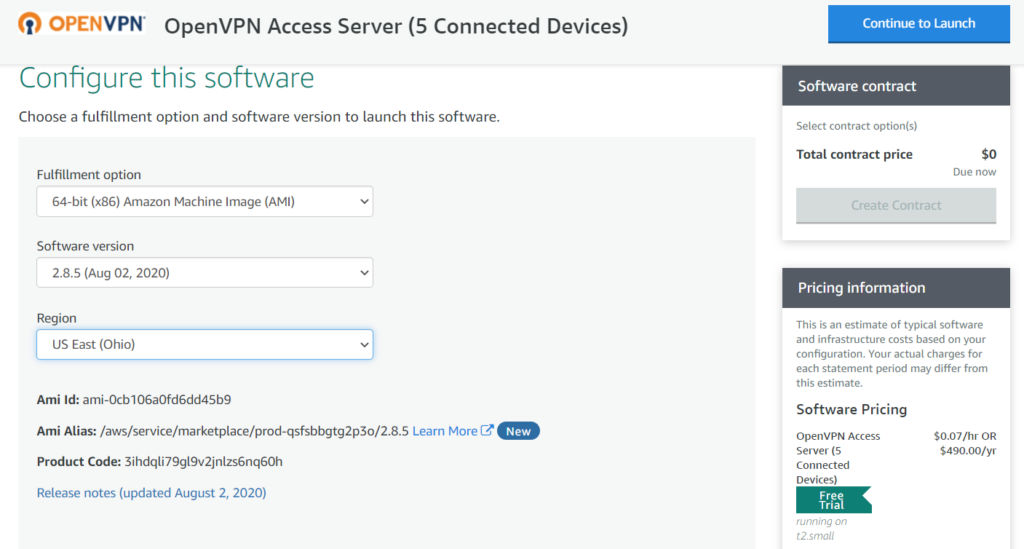
Then you want to choose the appropriate version and region that you want your host to sit in and then choose to launch using either the ec2 console or through the website.
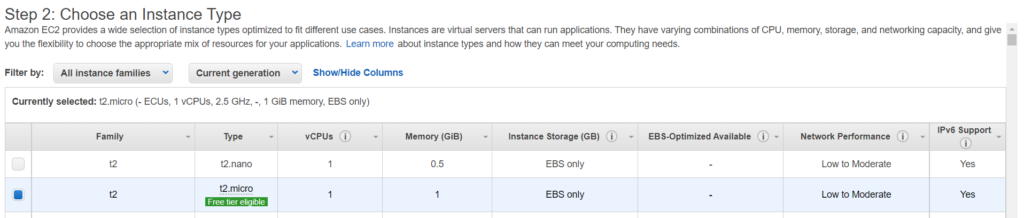
After being directed to the ec2 management console select the desired Ec2 instance size. For the purpose of this trial, we will stay on the free tier instance.
For the vpc settings and other configuration setups make sure to at least choose a vpc that is accessible from the internet. This will be how hosts are able to create an AWS Client VPN connection. When getting to the security group section let’s create a new security group to limit the access to the ports that we need.
If you launch from the marketplace, the security group may already be filled in with the needed ports for external access. If not, create a new aws security group and name it what you want. Then match your group with the same ports and ip ranges below.
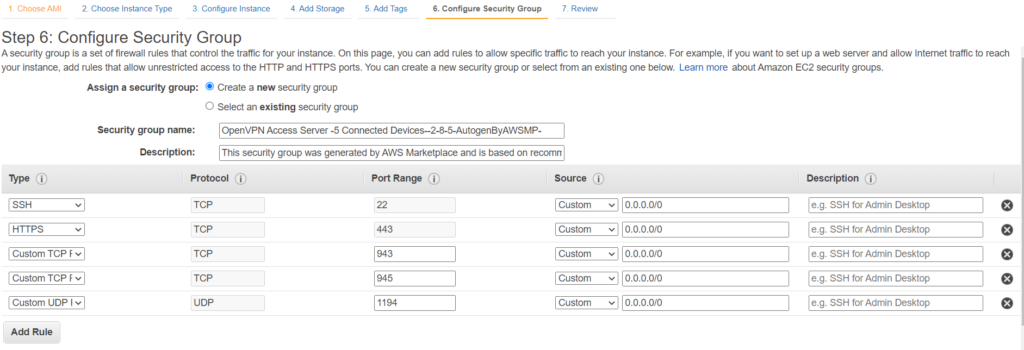
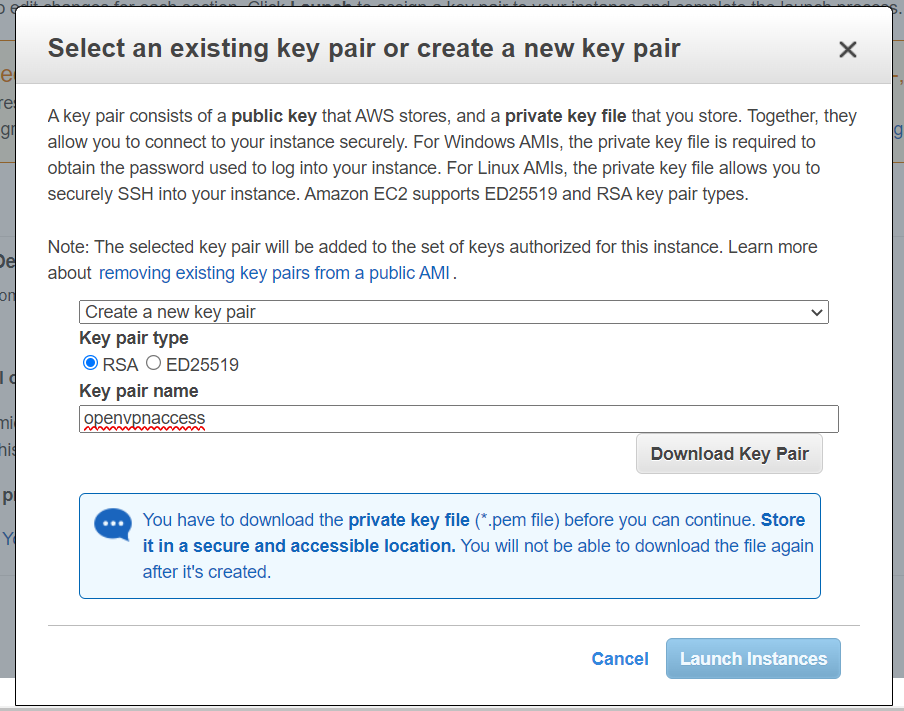
If all the required ports are not needed, then you can add or remove what you may need to improve the security of your openvpn server. When you get ready to launch you will need to create a new keypair that will give you the ability to gain access to your instance.
Setup an Elastic IP address on OpenVPN Instance
To enable remote access to your host you will need an Internet routable IP address that AWS provides for you. This public IP is used to access the admin web interface and as a VPN client’s tunnel formation endpoint.
Because the VPN appliance would be a single point of failure in this arrangement, this test solution might not be dependable in a production setting. As a result, when you’ve completed your test, you might want to investigate more robust choices, such as purchasing a second instance and setting both instances in high-availability (HA) mode.
On the OpenVPN website, read Active / Active High Availability Setup for OpenVPN Access Server for further information on how to set up a HA deployment.
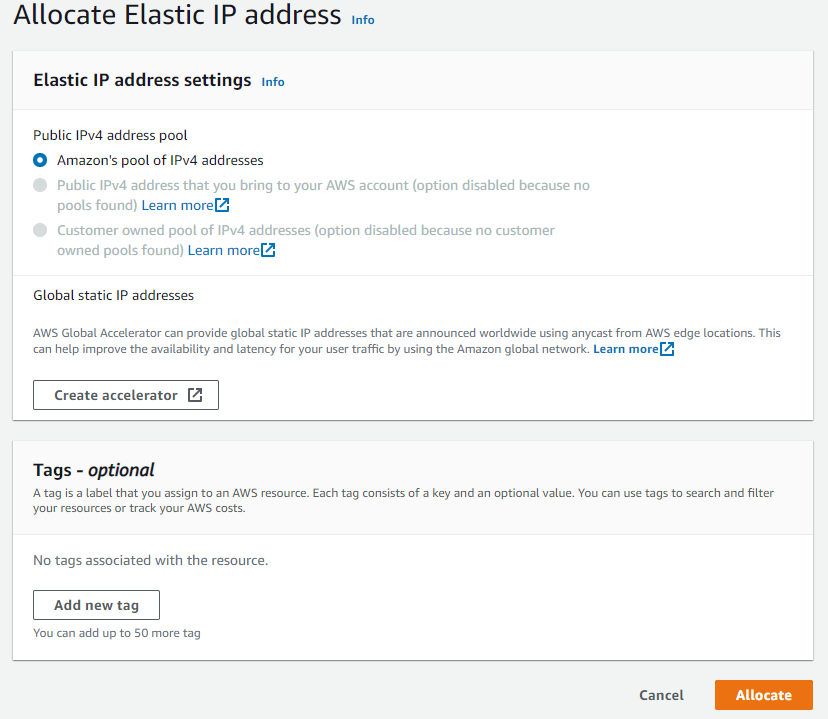
Open the network and security section on the ec2 dashboard and select Elastic IP and click allocate.
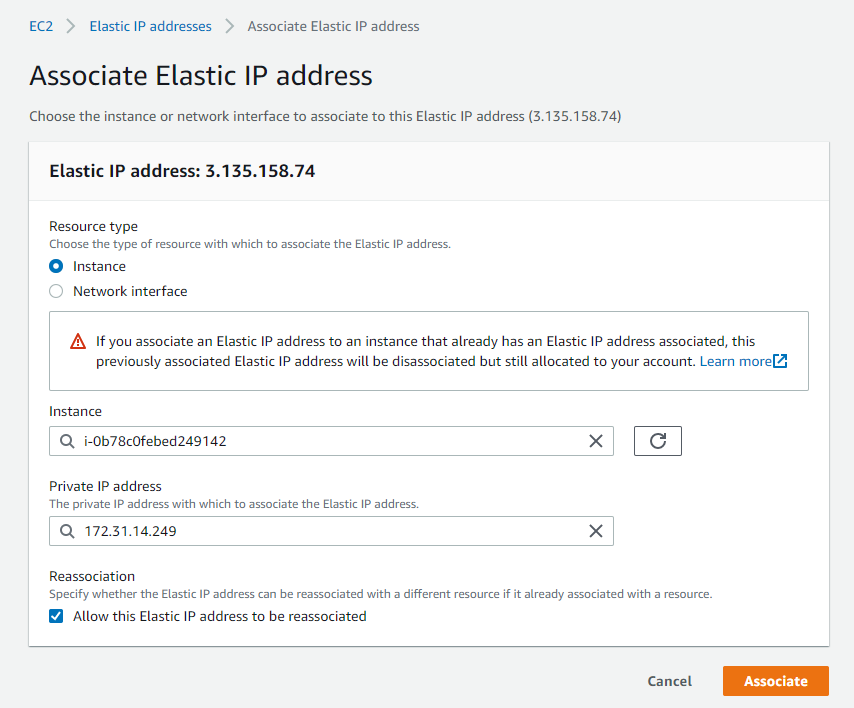
Then take that Elastic Ip Address and attach it to the running OpenVPN instance. Make sure to select allow this elastic ip address to be reassociated. This will enable you to keep the same ip address if your primary instance fails.
Accessing your OpenVPN Instance
Once you get everything configured in aws, you will need to finish configuring the openvpn software. To do so, use your pem file you downloaded when configuring your ec2 instance using a ssh client such as putty. These directions here should get you connected.
Before you can use the admin web interface, a setup wizard runs the first time you log in to the Access Server to allow you to configure startup parameters. You define an admin user and some network information in this step.
Once done with the ssh configuration, make sure to set a new password for the openvpn user if that is who you choose to use for your setup. Password can be changed using the command sudo passwd openvpn.
Setting up AWS Client VPN configuration options
Access the admin web interface for your OpenVPN server, point to the public Elastic IP address that you assigned and log in as the admin user that you set up at https://xxx.xxx.xxx.xxx/admin. Logging in brings you to the configuration page.
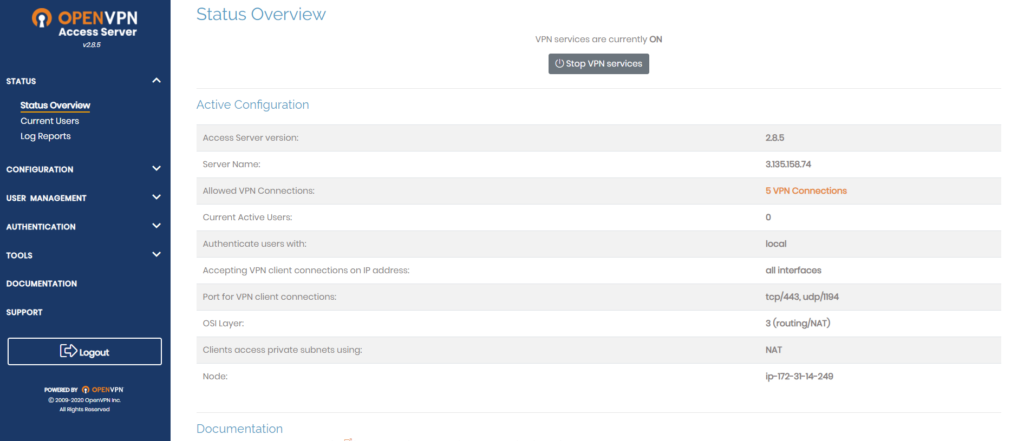
Default vpn settings provide clients who connect to the vpn a dynamic ip address which can be changed. This range must be different from your current networks. There are a couple of different settings that can be changed depending on your network use case such as:
- Specifying more private subnets the vpn users can connect to.
- Whether you want the vpn user’s internet traffic to route through the vpn tunnel
- DNS configurations for internal and external dns
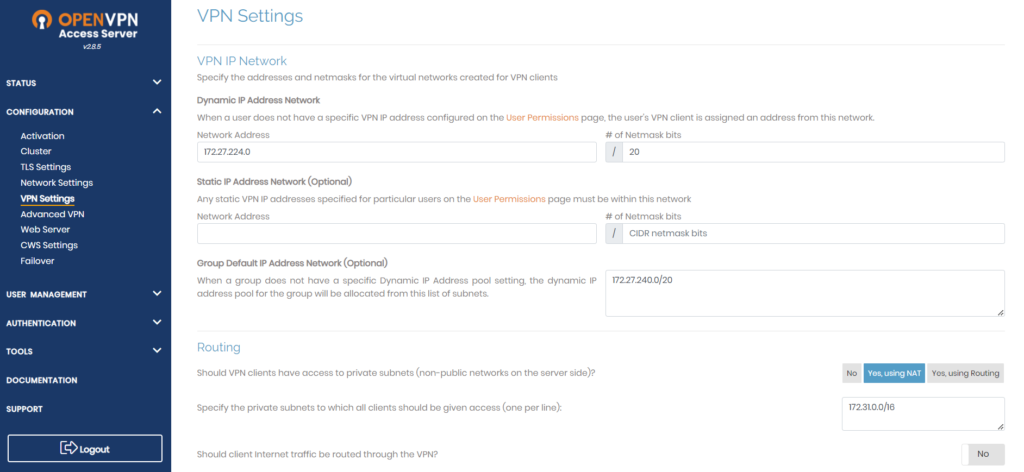
The routing is setup to map the clients ip address to one on the vpc to allow access to the resources. If you plan to choose the option “yes, using routing” then you must turn off “source/destination check” on the EC2 instance. This allows the instance to forward traffic to and from the clients.
Testing Client VPN Connection
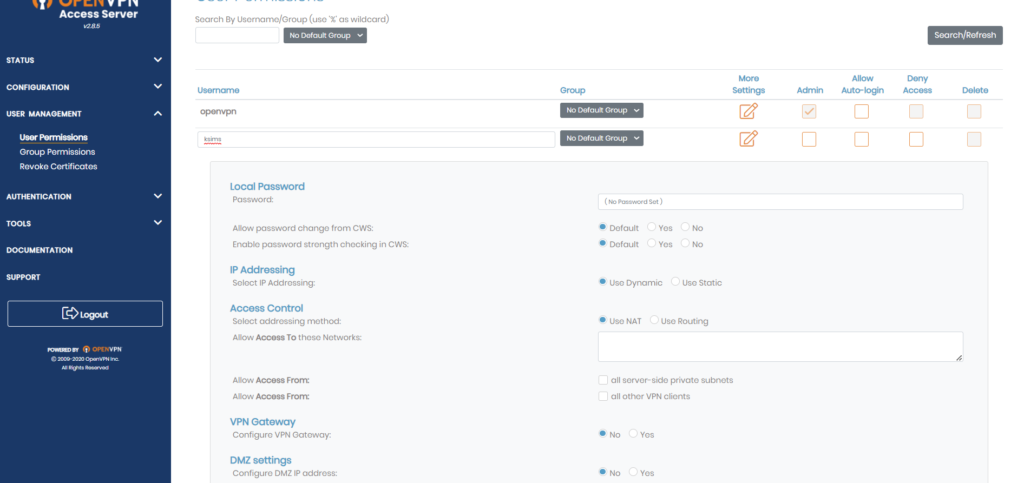
First you want to create a new user to login with. Then click more settings and provide a strong password for the end user. For testing purposes i kept everything default and saved the changes. The server will ask to restart the needed services next.
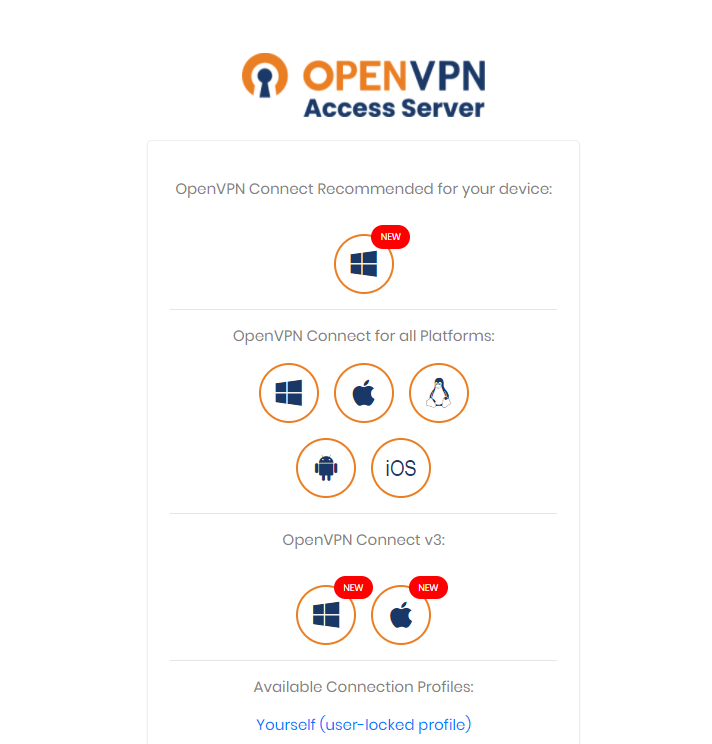
Go to the outside ip address of your vpn instance and sign in with the new username and password provided. Choose the best download option for your client device.
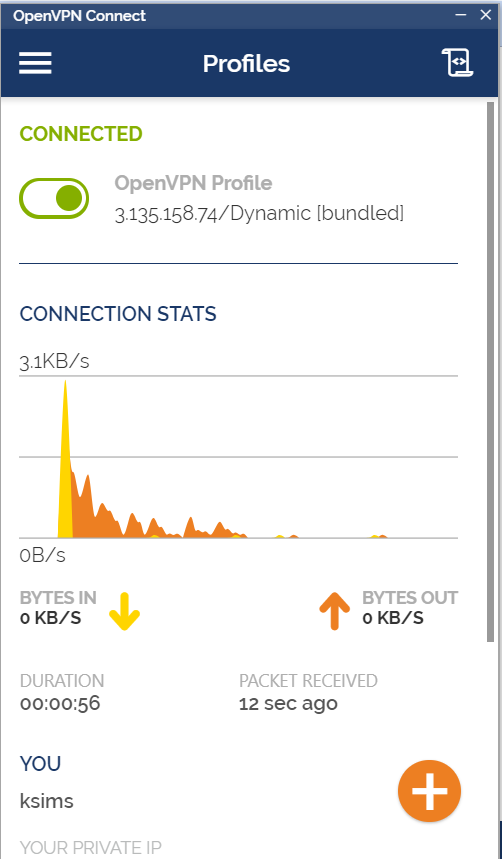
After the download, you may need to reopen openvpn connect and sign in again and click connect. Once you get connected you should be presented with a connection page and your network details. Attempt to now try and access any resources in your network at are not internet accessible or try using the private IP.
Conclusion
This article has presented you with detailed steps on how to configure an AWS Client vpn setup using Openvpn. You may give consumers private and secure access to your apps with this solution, even from faraway locations such as their homes and public areas.

This article may be a bit misleading as AWS Client VPN is a managed client-based VPN service. https://docs.aws.amazon.com/vpn/latest/clientvpn-admin/what-is.html
Yea i can see where it could be. At the time of writing I think my focus was more on the openvpn side and just didnt really pay attention to actually notice aws had a managed service.